Stellar Edge 3103804503 Cyber Flow is presented as a real-time cyber defense and network monitoring framework. It ingests multi-source telemetry, applies unified analytics, and correlates events to compute threat dwell time and risk. The approach emphasizes adaptive risk scoring, structured alerts, and coordinated containment workflows. It promises noise reduction and user experience preservation. The core question remains: how will its integration and metrics translate into measurable security outcomes for complex environments, and what are the practical implications to consider next?
What Is Stellar Edge 3103804503 Cyber Flow and Why It Matters
Stellar Edge 3103804503 Cyber Flow refers to a discrete cyber defense and network monitoring framework designed to detect, analyze, and respond to security events within complex enterprise environments.
Stellar Edge enables structured visibility, enabling control without constraint.
Cyber Flow emphasizes real time signals and coordinated responses, reducing threat dwell time, enhancing resilience, and empowering defenders with precise, actionable intelligence across heterogeneous networks.
How Cyber Flow Analyzes Real-Time Security and Performance Signals
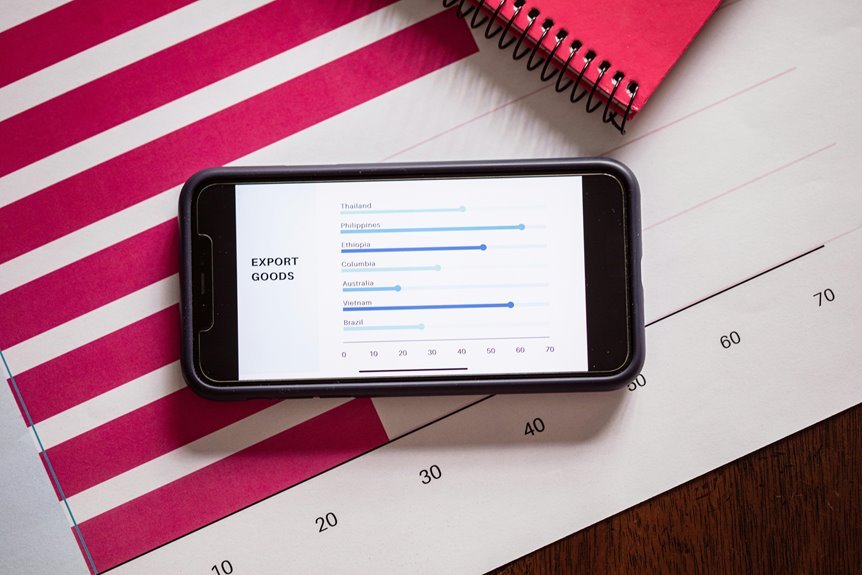
Cyber Flow analyzes real-time signals by ingesting multi-source telemetry from network devices, endpoints, and applications, then applying unified analytics to detect anomalies and correlate events across domains. It computes threat dwell time, aligns security performance with operational metrics, and quantifies risk in real time. The approach emphasizes visibility, reduces noise, and preserves user experience while enabling proactive defense and informed decision-making.
Practical Use Cases: Reducing Threat Dwell Time and Optimizing User Experience
Practical use cases for reducing threat dwell time and optimizing user experience illustrate how real-time analytics translate into actionable defense and performance gains.
In practice, threat dwell is shortened through rapid containment workflows, while user experience improves via responsive interfaces, adaptive risk scoring, and context-aware access.
Structured alerts and dashboards empower operators to balance security with seamless, unobtrusive, high-quality user experience.
Implementing Cyber Flow: Steps, Integration Points, and Success Metrics
Implementing Cyber Flow requires a disciplined, stepwise approach that aligns technology, processes, and metrics. The framework enumerates steps, coordinates integration points, and defines success metrics with rigor. Cyber flow relies on real time signals to couple data, actions, and outcomes. Clear governance, phased validation, and measurable objectives ensure robust deployment, while two word? coherence remains essential for adaptable freedom and accountability.
Conclusion
Stellar Edge 3103804503 Cyber Flow delivers precise, real-time insight by harmonizing multi-source telemetry into unified threat analytics and adaptive risk scoring. Its structured alerts and coordinated containment workflows translate complex signals into actionable responses, reducing dwell time without compromising user experience. By aligning detection, analysis, and response, the platform acts as a vigilant conductor, guiding enterprise security through the orchestration of visibility, automation, and measurable outcomes—like a lighthouse steadfastly guiding a ship through a digital fog.